You Can’t Protect What You Can’t See: Why UAE Businesses Need a Vulnerability Assessment Before Their Next IT Investment
There is a version of IT security that looks responsible from the outside. Firewall in place. Antivirus running. Backups scheduled. Staff told not to click suspicious emails.
And then there is IT security that has actually been tested.
The gap between the two is where most UAE businesses quietly sit not because they are careless, but because the tools that reveal your real exposure are often the last one’s organisations think to use. A vulnerability assessment and penetration test does not tell you what you have in place. It tells you whether what you have in place actually works.
That is a fundamentally different question. And for businesses operating in the UAE today, it is an increasingly important one to answer.
The Difference Between a Vulnerability Assessment and a Penetration Test
These two terms are used interchangeably so often that the distinction has become blurred even among IT professionals. They are related but not the same, and understanding the difference helps you use both more effectively.

Here is a straightforward comparison:
| Vulnerability Assessment | Penetration Test | |
| What it does | Scans and identifies known weaknesses across your environment | Simulates a real attack to actively exploit identified weaknesses |
| Depth | Broad — covers the full environment | Deep — focused on specific targets or scenarios |
| Frequency | Quarterly or after major changes | Annually or before major infrastructure changes |
| Output | Prioritised list of vulnerabilities with severity ratings | Detailed report of what was exploited, how, and what was accessed |
| Best used for | Ongoing visibility and compliance evidence | Validating controls and understanding real-world exposure |
| Who needs it | All businesses with IT infrastructure | Businesses handling sensitive data or in regulated sectors |
Think of a vulnerability assessment as a thorough health check — it tells you where the risks are. A penetration test is the stress test — it finds out what happens when those risks are actively exploited. Both are valuable. Neither replaces the other.
What a Vulnerability Assessment Actually Finds
Most businesses are surprised by the results of their first vulnerability assessment, not because the findings are catastrophic, but because the gaps are so ordinary. The most common issues we find across UAE business environments are not sophisticated zero-day exploits. They are the accumulated small decisions that made sense at the time.
Misconfigured systems and open ports
Devices and services that were set up quickly during a period of growth, with default credentials still in place or unnecessary ports left open. Each one is a potential entry point that serves no current business purpose.
Unpatched software across the estate
Not just operating systems, applications, firmware, network devices, and management tools that have fallen behind on updates. Attackers actively scan for known vulnerabilities in unpatched software because the exploit already exists and the fix has simply not been applied.
Overprivileged user accounts
Accounts with administrative access that no longer need it, former employees whose credentials were never deactivated, or service accounts with permissions that extend far beyond their function. Privilege sprawl is one of the most consistent findings in any UAE environment we assess.
Shadow IT and unmanaged devices
Applications installed without IT approval, personal devices connected to the corporate network, and cloud services being used outside of sanctioned processes. In the UAE’s fast moving business environment, shadow IT is particularly prevalent in organisations that have scaled quickly.
Weak network segmentation
As we covered in our previous post on ransomware resilience, flat network architecture means a compromise in one area can spread unchecked. A vulnerability assessment maps exactly where those lateral movement paths exist.
When to Run a Vulnerability Assessment, and When to Go Further
The right time for a vulnerability assessment is not after something goes wrong. It is before your next significant change and then regularly thereafter. Here are the business moments that should trigger one:
| Business Event | Why It Matters for VAPT |
| Before a cloud migration | Migrating unknown vulnerabilities into the cloud compounds risk significantly |
| Before a new office or site launch | New network segments and endpoints need to be assessed before go-live |
| After a significant headcount increase | More users, more devices, more endpoints the attack surface grows |
| Before a regulatory audit | NCA, DESC, and CBUAE frameworks expect documented evidence of assessments |
| After a merger or acquisition | Inherited infrastructure brings inherited vulnerabilities. Know what you’ve taken on |
| Annually as standard practice | Threat landscapes change; last year’s clean bill of health may not reflect today |
Penetration testing, by contrast, is most valuable when you want to understand your real-world exposure at depth typically annually for businesses in regulated sectors, or ahead of a significant infrastructure change where you need confidence that controls are working as intended.
What to Expect From the Process
One of the reasons businesses in the UAE defer vulnerability assessments is that the process feels opaque. What actually happens, and what does a report look like at the end of it?
Scoping
Before any assessment begins, the scope is agreed in detail which systems, networks, and applications are in scope, whether the test is conducted from inside or outside the network perimeter, and any systems that need to be excluded. A well scoped assessment is a far more useful one.
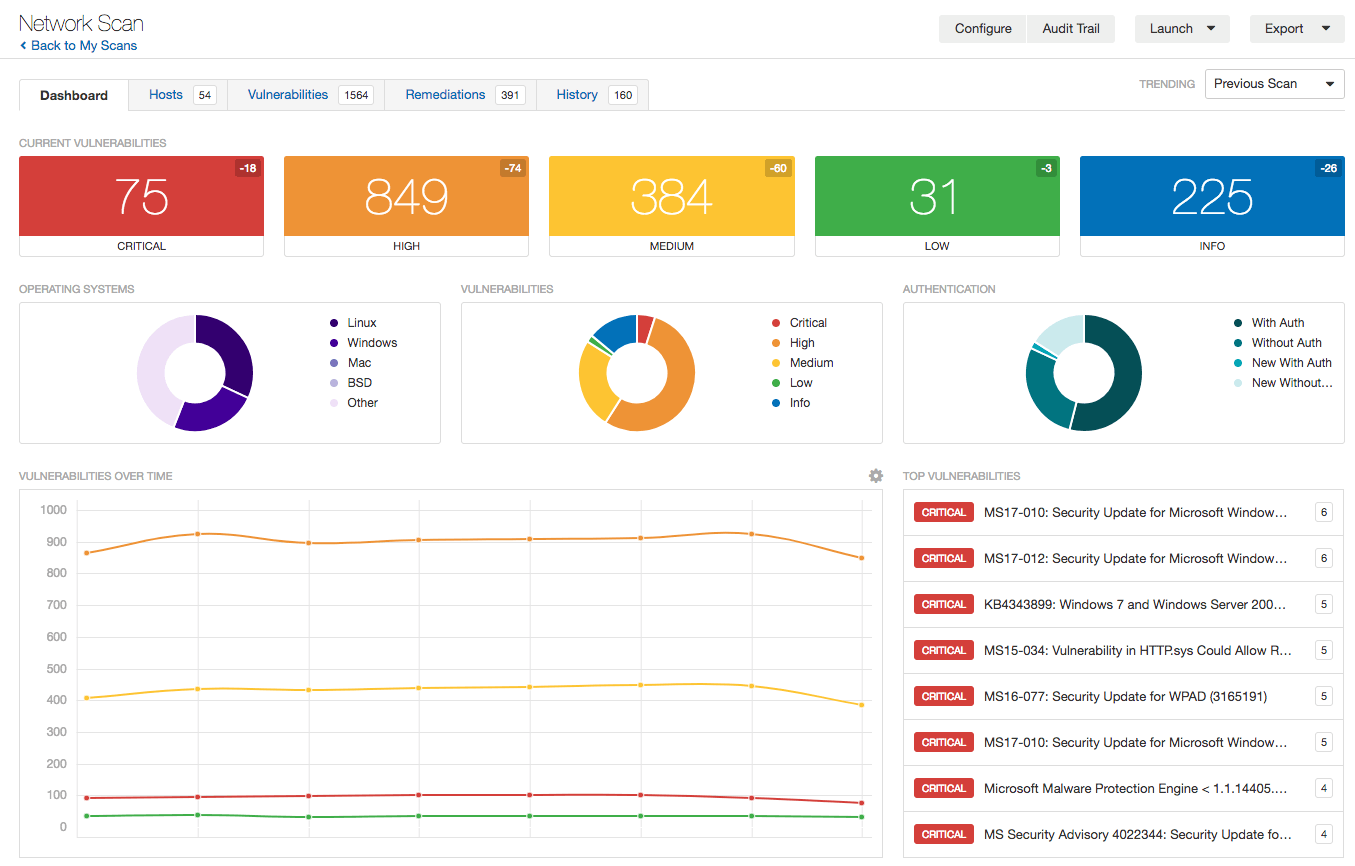
Discovery and scanning
Automated tools scan the in scope environment for known vulnerabilities, misconfigurations, and exposures. This is not a blunt instrument modern vulnerability scanners cross reference findings against databases of known exploits and assign severity ratings based on real world exploitability, not just theoretical risk.
Manual validation
Good assessors do not just hand you an automated report. Findings are manually reviewed to eliminate false positives, contextualise risks for your specific environment, and identify issues that automated tools miss. This step separates a meaningful assessment from a checkbox exercise.
The report
The output of a quality vulnerability assessment is a prioritised, actionable report not a list of hundreds of technical findings with no context. You should be able to see clearly: what the risk is, how severe it is, what an attacker could do with it, and what you need to do to fix it. Critical and high severity issues are addressed first; medium and low findings are documented for planned remediation.
Remediation and retest
The assessment does not end with the report. Once remediation work has been completed, a retest confirms that the vulnerabilities have been properly addressed and have not introduced new issues in the process.
A vulnerability assessment report is not bad news. It is a prioritised to-do list. The businesses that benefit most from the process are the ones that treat findings as actionable intelligence rather than a judgement on their IT team.
The Regulatory Dimension in the UAE

For many UAE businesses, vulnerability assessments are no longer just good practice they are an expectation embedded in the regulatory frameworks that govern their sector.
The UAE National Cybersecurity Authority (NCA) Cybersecurity Standards require organisations to implement processes for identifying and managing vulnerabilities across their environment. Documented evidence of regular assessments is increasingly expected not just policies that say assessments should happen.
The Dubai Electronic Security Center (DESC) Cloud Security Standard and related frameworks set specific requirements for entities operating within the Dubai Government ecosystem, including regular vulnerability assessments of cloud and on-premise infrastructure.
The Central Bank of UAE (CBUAE) Cyber Resilience Management Framework requires financial institutions to conduct regular vulnerability assessments and penetration tests as part of their cybersecurity programme with defined frequency requirements based on risk classification.
For businesses operating across multiple UAE free zones, the applicable frameworks may vary, but the direction of travel is consistent: regulators expect organisations to know their exposure, document it, and demonstrate that they are actively addressing it.
A vulnerability assessment does two things simultaneously: it improves your security posture and it produces the documented evidence that regulators increasingly want to see. It is one of the most efficient investments a UAE business can make against its compliance obligations.
What Good Findings Actually Mean
There is a tendency to dread what a vulnerability assessment might uncover as though finding something means the IT team has failed. This is the wrong frame.
Every business has vulnerabilities. The question is whether you know what they are before an attacker finds them, or after. A clean assessment with clear findings is not a condemnation it is an accurate picture of reality, which is precisely what you need to make good decisions.
The businesses that use vulnerability assessments most effectively treat each report as a management tool, not a report card. Findings go into a risk register. Remediation is tracked. Progress is measured. The next assessment shows improvement. Over time, the posture strengthens in a way that is documented, evidenced, and defensible.
That is what mature cybersecurity looks like in practice. Not an absence of vulnerabilities, but a disciplined process for finding and fixing them.
Where to Start
If your organisation has not had a vulnerability assessment in the past twelve months or has never had one the starting point is straightforward: scope a conversation with an experienced assessor about what your environment looks like and what a meaningful assessment would cover.
The output will give you something most IT teams genuinely do not have: a clear, prioritised, evidence based picture of where your real exposure sits. From there, every subsequent security investment becomes more targeted and more effective.
You cannot protect what you cannot see. A vulnerability assessment is how you start seeing clearly.

Find Out Where Your Infrastructure Stands
Candor’s VAPT service gives UAE businesses a clear, prioritised picture of their security exposure and a practical plan to address it. No jargon, no unnecessary alarm. Just an honest assessment from a team that understands the regional landscape.
👉 Get in touch with our team today.